Fiber Network Security: Essential Tools to Safeguard Your Network’s Integrity
Wiki Article
Why Information and Network Safety And Security Ought To Be a Top Priority for each Organization
Increasing Cyber Danger Landscape
As organizations increasingly count on digital frameworks, the cyber threat landscape has actually grown substantially more complicated and dangerous. A wide range of advanced strike vectors, including ransomware, phishing, and advanced persistent threats (APTs), posture substantial risks to sensitive data and operational connection. Cybercriminals utilize evolving innovations and strategies, making it essential for organizations to continue to be aggressive and attentive in their protection actions.The expansion of Internet of Points (IoT) tools has additionally exacerbated these difficulties, as each linked tool stands for a potential entry point for destructive stars. Additionally, the rise of remote job has actually expanded the assault surface, as staff members gain access to corporate networks from numerous places, often making use of individual devices that might not follow rigorous protection methods.
Moreover, regulatory conformity requirements remain to evolve, necessitating that organizations not just shield their data yet likewise demonstrate their commitment to securing it. The boosting integration of expert system and machine learning right into cyber protection methods offers both challenges and chances, as these technologies can improve hazard discovery however may likewise be manipulated by adversaries. In this atmosphere, a adaptive and robust protection position is essential for alleviating dangers and making certain organizational durability.
Financial Effects of Data Breaches
Data violations lug significant monetary effects for companies, typically causing costs that extend far past prompt removal efforts. The initial costs commonly consist of forensic investigations, system fixings, and the application of improved protection actions. The monetary after effects can better rise via an array of added variables.One significant concern is the loss of revenue stemming from lessened consumer trust fund. Organizations might experience reduced sales as customers look for even more safe options. In addition, the lasting influence on brand name reputation can result in decreased market share, which is difficult to quantify yet greatly impacts earnings.
Additionally, organizations may encounter boosted expenses pertaining to customer alerts, credit report tracking services, and possible compensation cases. The monetary concern can also include potential boosts in cybersecurity insurance costs, as insurance firms reassess danger complying with a violation.
Regulatory Conformity and Legal Risks
Organizations encounter a myriad of regulative conformity and legal dangers following a data violation, which can considerably make complex recovery efforts. Numerous laws and policies-- such as the General Data Defense Regulation (GDPR) in Europe and the Medical Insurance Portability and Responsibility Act (HIPAA) in the USA-- mandate strict guidelines for data defense and violation notification. Non-compliance can lead to hefty fines, lawsuits, and reputational damages.
Moreover, organizations must navigate the complicated landscape of state and government regulations, which can differ considerably. The capacity for class-action lawsuits from impacted stakeholders or consumers better exacerbates legal difficulties. Business often face scrutiny from regulatory bodies, which may impose additional penalties for failings in data administration and safety.
Along with monetary repercussions, the legal ramifications of an information violation might demand significant financial investments in lawful advise and conformity resources to manage examinations and removal initiatives. Comprehending and sticking to appropriate policies is not just an issue of legal obligation; it is crucial for protecting the company's future and keeping functional stability in an increasingly data-driven setting.
Structure Client Depend On and Loyalty
Regularly, the structure of customer count on and loyalty rest on a business's commitment to information safety and security and privacy. In an age where data violations and cyber dangers are increasingly widespread, consumers are extra discerning about just how their personal details is handled. Organizations that focus on robust data defense determines not just protect delicate information yet also foster an atmosphere of depend on and openness.When consumers regard that a business takes their data safety seriously, they are more probable to take part in long-lasting connections with that brand name. This trust fund is strengthened through clear communication about information techniques, consisting of the sorts of info accumulated, exactly how it is utilized, and the steps required to secure it (fft perimeter intrusion solutions). Companies that adopt a positive approach to safety can separate themselves in an affordable marketplace, causing raised customer commitment
Additionally, organizations that show accountability and responsiveness in case of a safety and security occurrence can transform prospective crises right into possibilities for enhancing client partnerships. By continually prioritizing data safety and security, services not only protect their possessions but additionally cultivate a dedicated consumer base that feels valued and protect in their communications. By doing this, information protection becomes an indispensable part of brand name integrity and customer satisfaction.
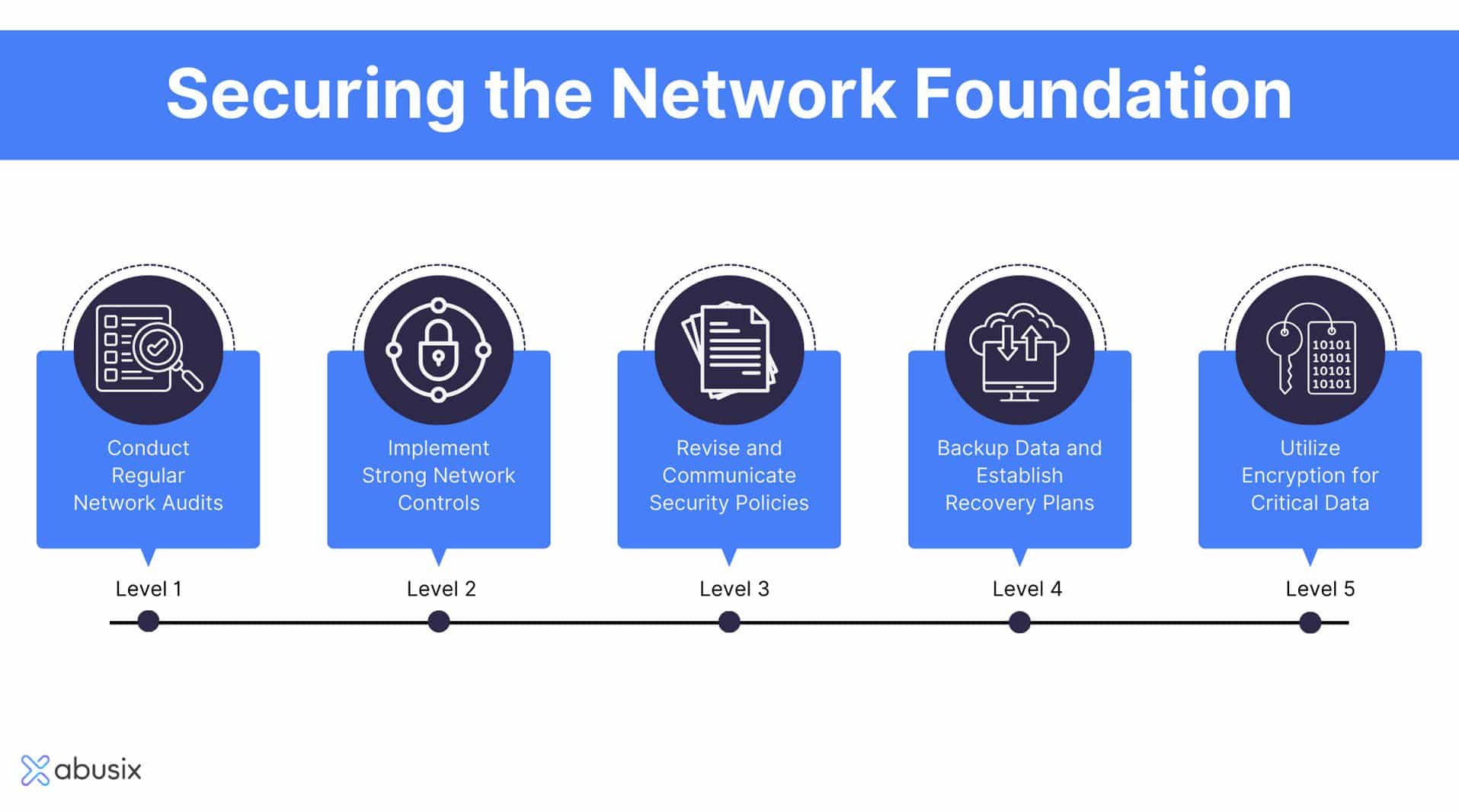
Important Techniques for Defense
In today's landscape of progressing cyber risks, executing essential strategies for security is essential for securing delicate info. Organizations should embrace a multi-layered security method that consists of both technological and human aspects.First, releasing advanced firewall programs and invasion discovery systems can help keep track of and block destructive tasks. Normal software program updates and patch monitoring are essential in resolving vulnerabilities that might be exploited by assailants.
2nd, staff member training is critical. Organizations ought to conduct routine cybersecurity recognition programs, enlightening team about phishing scams, social engineering methods, and secure browsing methods. A knowledgeable labor force is an effective line of protection.
Third, information security is vital for safeguarding sensitive information both in transit and at rest. fft perimeter intrusion solutions. This guarantees that also if information is intercepted, it stays inaccessible to unauthorized users
Final Thought
In conclusion, prioritizing data and network safety and security is vital for organizations navigating the progressively complicated cyber danger landscape. The economic repercussions of data violations, combined with rigorous regulatory conformity requirements, emphasize the requirement for data cyber security robust protection actions. Furthermore, guarding sensitive info not only reduces dangers however additionally improves client count on and brand name commitment. Executing crucial techniques for protection can make sure organizational strength and promote a safe and secure setting for both organizations and their stakeholders.In an age marked by an enhancing frequency and class of cyber hazards, the essential for companies to focus on information and network safety and security has actually never ever been more important.Frequently, the structure of customer trust and loyalty copyrights on a company's dedication to data security and privacy.When customers regard that a business takes their information safety and security seriously, they are a lot more likely to involve in long-lasting relationships with that brand. By consistently prioritizing information safety, services not just shield their properties however also cultivate a loyal client base that feels valued and secure in their communications.In conclusion, prioritizing information and network safety and security is important for organizations navigating the increasingly complicated cyber hazard landscape.
Report this wiki page